What Happened During Nintendo's Data Breach in 2020?
Nintendo has had a run of cyberattacks in recent years. In 2017 they were infamously hacked by a security researcher, Zammis Clark, who stole over two terabytes of data, including game source files, prototypes, game emulators, unreleased products, and more, some of which dated back to the 80s!
In April 2020, Nintendo was again at the center of a cyber-security controversy, this time involving 300,000 Nintendo Network ID (NNID) for Nintendo Switch accounts. Initially, Nintendo claimed it was only 160,000, but it discovered another 140,000 compromised accounts after further investigation.
While more than 300,000 Nintendo users were hacked, less than 1% were used to make fraudulent transactions. Nintendo has been vague about how attackers acquired user logins but did mention in a statement that data was "obtained illegally from other than our service by some other means."
Get a free trial of TeamPassword to bolster your business security and effectuate efficiency.
Table of Contents
Nintendo Breach Timeline of Events
- April 9, 2020 - Much to the confusion of its followers, Nintendo randomly Tweets: "You can help secure your Nintendo Account by enabling 2-Step Verification." with a link to instructions.
- April 19, 2020 - Founding editor of LootPots, a Nintendo fansite Tweets: "I suspect Nintendo may have had a major security breach. My account was accessed numerous times overnight. My password is a unique string, and my PC is definitely clean (not that I ever login via it). Lots of similar reports on Reddit/Twitter. Unlink PayPal & enable 2FA folks!"
- April 24, 2020 - Nintendo releases an official statement confirming 160,000 accounts have been compromised.
- April 27, 2020 - Nintendo confirms they have discovered another 140,000 accounts, taking the total to 300,000.
What Account Information Was Compromised?
During the 2020 Nintendo Network ID (NNID) breach, sensitive personal information of affected users was exposed. According to official statements from Nintendo, the compromised data included:
- Full name of the account owner
- Email address
- Date of birth
- Country or region of residence
While this information did not include sensitive financial details like full credit card numbers, it still posed a significant risk to users, especially considering the potential for identity theft and phishing attacks. Although billing information was not directly exposed in the breach, Nintendo confirmed that stored payment methods, such as linked PayPal accounts or credit cards, could still be exploited by attackers to make unauthorized purchases through platforms like the My Nintendo Store or Nintendo eShop.
How Did Hackers Access Nintendo User Accounts?
For "security reasons," Nintendo hasn't disclosed how hackers access NNID accounts, but they do confirm there wasn't a breach of their servers, leaving three possible scenarios.
Credential Stuffing
Hackers use usernames (or email addresses) and passwords stolen from one application to perform automated large-scale application logins. These credentials are often stolen from the servers of games or applications with weak security.
Hackers rely on the fact that many people use the same username and password for multiple accounts. One possibility is that hackers may have gained access to a chatroom or application frequented by Nintendo users and stolen login credentials.
Cybercriminals would then need to test each username and password and see if anyone has used the same credentials for their Nintendo account.
We know that Nintendo encouraged users to use different passwords for their NNID and Nintendo Account to minimize the risk of credential stuffing.
Phishing
Another likely scenario, and one that's very common, is that Nintendo users may have been victims of a phishing attack. In a phishing attack, cybercriminals use a "spoof" message (text, email, etc.) to trick a user into clicking a link or revealing sensitive data.
On first inspection, phishing attacks are challenging to identify because hackers will mimic correspondence or even build a replica application or website login.
Brute Force Attack
A brute force attack is essentially a guessing game where hackers systematically try passwords until they gain access. They often start with common phrases and combinations and then use phrases relevant to a user's name or personal information.
Nowadays, most websites and applications prevent brute force attacks by limiting the number of times you can enter a correct password or requiring two-factor authentication (2FA).
The Fallout of Nintendo's User Breach
Nintendo users were understandably upset, taking to Twitter and Reddit to vent their frustrations. Not only was this the second major breach for Nintendo in the space of three years, but the Japanese giant's lackluster response seemed to fuel anger and frustration.
Users were given no real explanation of how this happened, which would help knowing where they might be vulnerable.
Nintendo did offer to cancel and refund any fraudulent purchases, but according to several Reddit posts, this has not been easy with Nintendo denying some requests.
Nintendo now requires users to use two-factor authentication to prevent this type of breach from happening again.
Protecting Yourself Against Unauthorized Logins
While companies are responsible for protecting our data, we must also take responsibility to protect ourselves. That means better password management.
Companies will do everything they can to avoid refunds, so if they can prove you were negligent, there's a high likelihood you might never recoup some or all of your losses.
Stronger, Secure Passwords
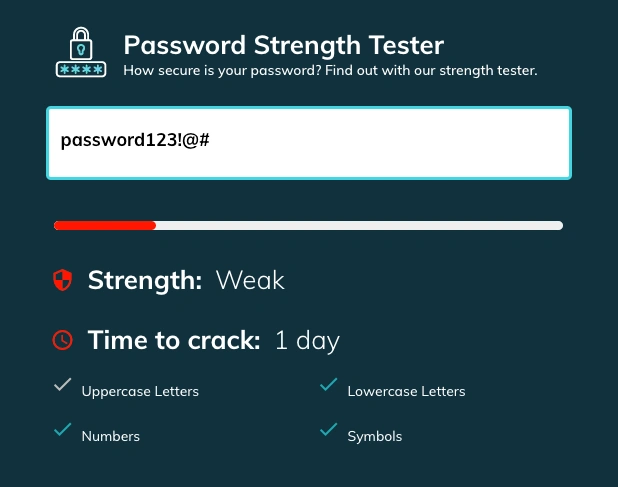
The first step is creating secure passwords for all of your accounts. A secure password should be unique, complicated, and ideally no less than 12 characters, so it's near impossible to guess.
One way to create stronger passwords is by using a secure password generator. These password generators produce a complicated series of randomized characters for you to copy/paste.
With TeamPassword, you get a built-in password generator capable of creating 32-character secure passwords. You can choose to include uppercase, lowercase, numbers, and symbols to ensure you get robust passwords every time.
Create a Different Password for Every Account
Another huge mistake people make, using the same password across multiple accounts. Even if you have a 32-character, ultra-secure password, you should never use it more than once.
If a hacker steals that password during a breach or you fall victim to a cyberattack, criminals will have access to all of your accounts.
By creating a separate password for every account, website, and application, you're limiting your exposure and minimizing potential losses.
Two-Factor Authentication (2FA)
Once you have secure passwords and use different credentials for every login, you'll want to add another layer of security. Two-factor authentication (2FA) will prevent anyone from accessing your accounts, even if they have your login credentials.
What is 2FA, and How Does it Work?
2FA is a two-step process for logging into an account. The primary step is your password, while the second step is an action you need to take, which could include:
- Possession factor - an authentication method linked to a person such as a 2FA device, text message, email, or application on one of your devices. For example, when logging in to your bank account, you might receive a text message with a code to enter after your password.
- Knowledge factor - authentication through a memorable word or phrase. For example, your mother's maiden name or the name of your best friend in high school.
- Biometric factor - authentication through fingerprints, retina shape, or facial and voice recognition.
Most applications use Google Authenticator, Authy, or another software token authenticator app (possession factor) to facilitate 2FA, but some companies might send a text or email or have their own applications or devices. Google Authenticator is popular because it's free and available for iOS and Android.
TeamPassword uses Google Authenticator for 2FA, and you can also generate backup codes to ensure you never get locked out.
TeamPassword - A Comprehensive Password Management Solution for Businesses
TeamPassword offers an all-in-one solution to manage and secure your passwords, streamlining password creation, storage, and sharing processes. By incorporating advanced security features such as two-factor authentication (2FA) and backup codes, TeamPassword ensures that your sensitive data remains safe from unauthorized access and cyber threats.
Cutting-Edge Encryption and Security
TeamPassword utilizes industry-leading encryption standards to safeguard your passwords and other sensitive information. With the most up-to-date encryption technology, your data remains fully protected whether it’s at rest or in transit, offering peace of mind in an increasingly complex digital landscape.
Access from Anywhere, on Any Device
TeamPassword provides flexible access to your passwords, allowing you to manage credentials from any device, whether you're using a desktop, laptop, or mobile. The platform supports browser extensions for Chrome, Firefox, and Safari, enabling you to log into your accounts quickly and securely, no matter where you are.
Collaborative Sharing for Teams
A critical feature of TeamPassword is its ability to facilitate secure password sharing among team members. Instead of emailing or texting sensitive information, you can share login credentials seamlessly and securely within the platform. When team members no longer need access, you can revoke permissions with a single click, ensuring that access is granted and revoked efficiently, maintaining maximum control over your security environment.
Built-In Password Generator for Stronger Security
TeamPassword’s built-in password generator helps you create complex, secure passwords with customizable options ranging from 12 to 32 characters. You can include upper and lowercase letters, numbers, and special symbols, ensuring your passwords are highly resistant to brute force attacks. Once generated, passwords are automatically stored in the application, eliminating the risk of misplacing or forgetting them.
Detailed Activity Logging and Real-Time Alerts
Managing multiple accounts and users can be challenging without proper oversight. TeamPassword provides comprehensive activity logs that allow you to track login attempts, shared passwords, and any modifications in real-time. Additionally, customizable email alerts notify you of critical activities, making it easier to monitor access to sensitive data, especially for high-security accounts and applications.
By consolidating password management, access control, and collaboration into one platform, TeamPassword simplifies the process of securing and managing credentials across teams. With robust security features and intuitive user interfaces, it’s an essential tool for businesses and individuals looking to fortify their password practices.
Avoid becoming another data-breach statistic. Try TeamPassword with a free trial today and take control of your password management!
Enhance your password security
The best software to generate and have your passwords managed correctly.