What Are the SOC 2 Password Requirements?
If you are a service organization that handles sensitive customer data, you may have heard of SOC 2 compliance. SOC 2 is a set of standards that evaluates how well you protect your data from unauthorized access, misuse, or loss. Achieving SOC 2 compliance can boost your reputation, trustworthiness, and customer satisfaction.
One of the key aspects of SOC 2 compliance is password management. Passwords are the first line of defense against cyberattacks, and they need to be strong, secure, and updated when necessary. In this blog post, we will explain what SOC 2 password requirements are and how you can meet and exceed them with some best practices.
Here are the key things you need to know about SOC 2 password requirements:
- SOC 2 is based on five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
- Password requirements fall under the security criterion, which covers logical and physical access controls.
- Passwords should be at least 12-16 characters long and include a mix of uppercase and lowercase letters, numbers, and special characters.
- Accounts should be locked out after five or more failed login attempts.
Table of Contents
An Overview of SOC 2
SOC 2 is a report that provides assurance on how well a service organization manages its customer data. It is issued by an independent auditor who evaluates the organization's controls against the Trust Services Criteria (TSC) established by the American Institute of Certified Public Accountants (AICPA).
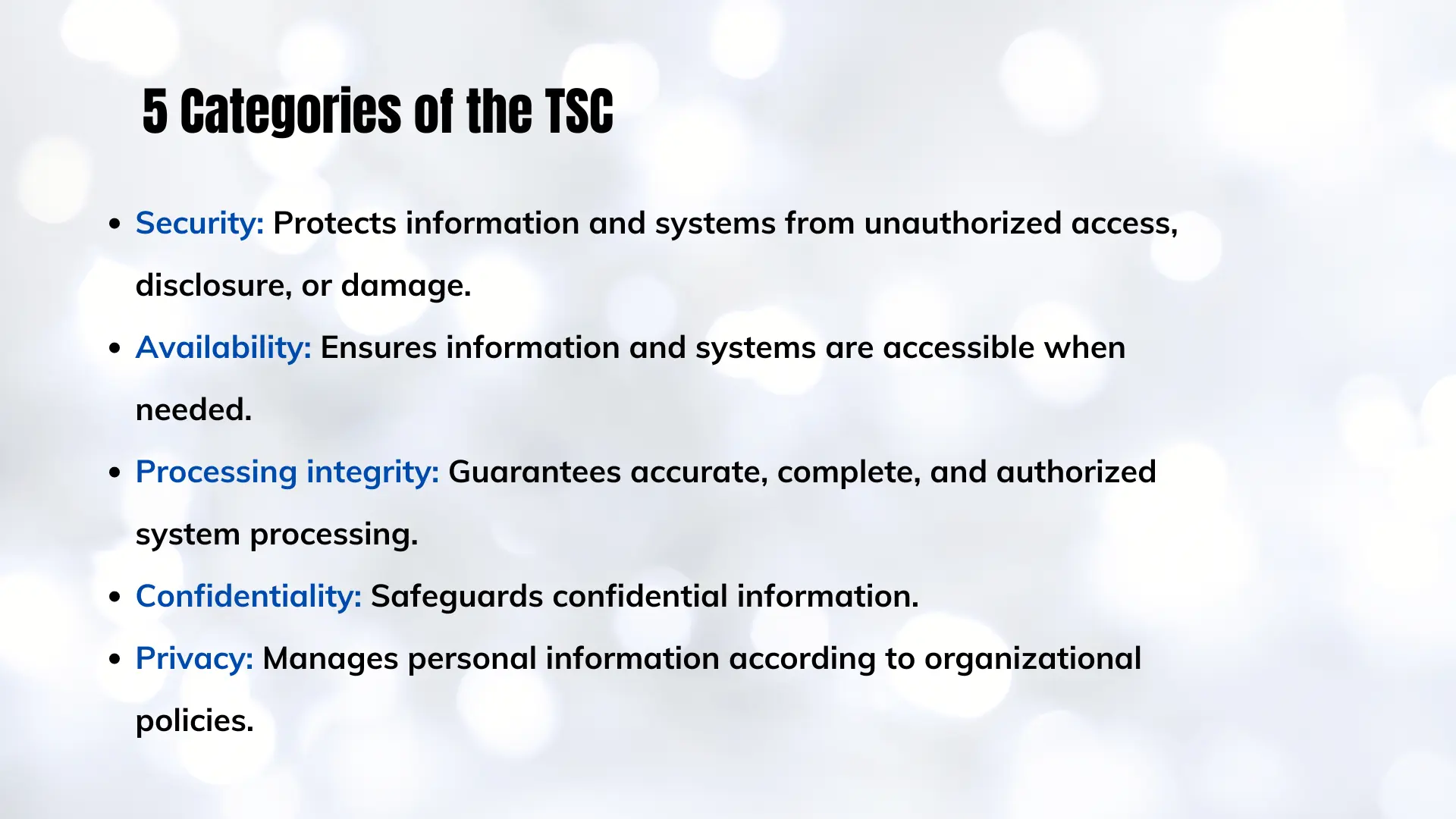
The TSC has five categories that cover different aspects of data security:
- Security - ensures the protection of information and systems from unauthorized access, disclosure, and damage that could jeopardize availability, integrity, confidentiality, and privacy, impacting the entity's objectives.
- Availability - guarantees that information and systems are accessible to support the entity's goals.
- Processing integrity - ensures that system processing is accurate, timely, valid, complete, and authorized, aligning with the entity's objectives.
- Confidentiality - safeguards designated confidential information in alignment with the entity's objectives.
- Privacy - governs the collection, use, retention, disclosure, and disposal of personal information to meet the entity's objectives.
Depending on the nature and scope of their services, organizations may choose to comply with one or more of these criteria. However, security is the most common and essential criterion for all service organizations that handle customer data.
Why Password Requirements Are Crucial in SOC 2
Passwords are one of the most basic and important controls for securing data. They prevent unauthorized access to systems, applications, databases, networks, devices, and other resources that store or process customer data.
However, passwords are also one of the most vulnerable and exploited controls by cybercriminals. According to Verizon's 2020 Data Breach Investigations Report, 80% of hacking-related breaches involved compromised or weak credentials. Some of the common ways that passwords can be compromised include:
- Brute-force attacks: Trying different combinations of characters until the correct password is found.
- Dictionary attacks: Trying common or predictable passwords based on words, names, dates, or other information.
- Phishing attacks: Tricking users into revealing their passwords through fake emails, websites, or messages.
- Keylogging attacks: Capturing the keystrokes of users when they type their passwords.
- Credential stuffing attacks: Using stolen or leaked passwords from one site or service to access another.
These attacks can have serious consequences for both the service organization and its customers. They can result in data breaches, identity theft, fraud, ransomware, malware, reputation damage, legal liability, and financial losses.
Therefore, it is crucial for service organizations to implement and enforce strong password requirements as part of their SOC 2 compliance. These requirements help to reduce the risk of password compromise and enhance the security of customer data.
SOC 2 Password Requirements Explained
SOC 2 does not specify exact password requirements for service organizations. Instead, it provides general guidelines and best practices based on the AICPA's Trust Services Criteria and the Committee of Sponsoring Organizations of the Treadway Commission's (COSO) framework for enterprise risk management.
According to these guidelines and best practices, service organizations should consider the following password requirements:
Password Length & Complexity
Password length and complexity are two factors that affect the strength and security of a password. The longer and more complex a password is, the harder it is to guess or crack.
A common recommendation for password length is to use at least 12 characters. This is based on the assumption that an attacker can try 1 trillion guesses per second, which would take about 200 years to crack a 12-character password .
However, length alone is not enough. Passwords should also include a mix of uppercase and lowercase letters, numbers, and special characters. This increases the possible combinations of characters and makes passwords more unpredictable. For example, a password like "password123" is easy to guess and crack, even if it meets the minimum length requirement.
Password Rotation & History
Password rotation and history are two factors that affect the freshness and uniqueness of a password.
In the past, it was commonly suggested to change passwords every 90 days. However, this is no longer recommended. It is better to create one strong, secure, and unique password, and typically only change it in the event of a known breach.
Never reuse passwords.
For example, a password like "86c1^Y#m'DHc=c_N" may be strong and complex, but if it is used for multiple accounts or services, it increases the risk of compromise. A better practice would be to use different passwords for different accounts or services and change them regularly.
Account Lockouts
Account lockouts are a factor that affects the security and usability of a password. They prevent an attacker from trying multiple passwords until they find the correct one.
A common recommendation for account lockouts is to lock out an account after three or more failed login attempts. This is based on the assumption that an attacker can try thousands of passwords per minute using automated tools or scripts.
However, account lockouts also have drawbacks. They can inconvenience legitimate users who forget their passwords or make typos. They can also be abused by malicious actors who deliberately lock out users to cause denial-of-service attacks.
Therefore, service organizations should balance account lockouts with other measures such as:
- Implementing multi-factor authentication (MFA) to require additional verification beyond passwords.
- Monitoring login attempts and sending alerts or notifications to users or administrators when suspicious activity is detected.
- Providing self-service options or support channels for users to reset their passwords or unlock their accounts.
Best Practices to Meet and Exceed SOC 2 Password Requirements
Training Employees
In the context of SOC 2 compliance, it is imperative to educate employees on the creation of robust passwords. This entails conducting comprehensive training sessions aimed at imparting knowledge about crafting strong and secure passwords.
The objective of such training is to emphasize the importance of avoiding easily guessable information, such as birthdays or simple sequences like "password123." Employees should be encouraged to create passwords that are complex, unique, and resistant to brute-force attacks. The ultimate goal is to establish a formidable defense against unauthorized access.
Using a Password Manager
Password managers are indispensable tools for secure password management. They serve as secure repositories for storing and accessing passwords, minimizing the risk of compromise.
There are many good solutions in this domain. One of the best password managers for teams is TeamPassword. It streamlines password management by allowing controlled access to credentials, easy and secure sharing, and industry-standard vault encryption. Access can be tailored to specific team members, reducing the chances of unauthorized access.
TeamPassword also offers features such as password generation, expiration reminders, and audit logs, enhancing overall security and compliance efforts.
Implementing Two-Factor Authentication
To fortify password-based security measures, organizations should consider implementing Two-Factor Authentication (2FA). 2FA introduces an additional layer of security, significantly enhancing the difficulty of unauthorized access.
With 2FA, even if an intruder gains access to a password, they would require a second, time-sensitive code typically sent to a mobile device or email. This supplementary step serves as a substantial barrier against unauthorized entry, aligning seamlessly with SOC 2's stringent security requirements.
Organizations are advised to employ 2FA wherever applicable, particularly for systems and data repositories that hold sensitive information.
Other Critical SOC 2 Requirements for Compliance
While password security is a pivotal aspect of SOC 2 compliance, it is essential to recognize that overall compliance encompasses a wider spectrum of security measures.
Firewalls: One of the cornerstone measures in the SOC 2 compliance framework is the deployment of robust firewalls. Firewalls act as formidable barriers against external threats, acting as the first line of defense for your systems and data. By analyzing incoming and outgoing network traffic, firewalls are instrumental in preventing unauthorized access, malicious attacks, and data breaches.
Intrusion Detection Systems (IDS): In today's dynamic threat landscape, where cyberattacks constantly evolve, intrusion detection systems are indispensable. These systems function as vigilant sentinels, tirelessly monitoring network activity. They use sophisticated algorithms to identify anomalies and potential security breaches. When unusual patterns or suspicious activities are detected, IDS sends out alerts, allowing your security team to respond swiftly and mitigate threats before they escalate.
Routine Security Audits: SOC 2 compliance requires an ongoing commitment to security. Routine security audits are essential to assess and validate the effectiveness of your security controls and policies. These audits provide valuable insights into areas that may need improvement and ensure that your security measures are up to date and in compliance with evolving standards.
Data Encryption: Encryption is a non-negotiable component of SOC 2 compliance. It ensures that sensitive data is protected during transmission and storage. Data encryption translates information into a code that can only be deciphered with the appropriate encryption key. This security measure safeguards against data interception and unauthorized access, maintaining the confidentiality and integrity of your data.
Stringent Access Controls: Controlling who has access to your systems and data is fundamental to SOC 2 compliance. Implementing stringent access controls ensures that only authorized individuals can access sensitive information. This includes user authentication, role-based access control, and continuous monitoring of user activity to detect any suspicious actions.
In conclusion, SOC 2 compliance requires a multifaceted approach to security. While strong password management is essential, it should be integrated into a broader security framework that includes firewalls, intrusion detection systems, routine audits, data encryption, and strict access controls. By addressing these critical components comprehensively, organizations can establish a robust security posture and meet the rigorous standards of SOC 2 compliance.
Elevate your password security and streamline SOC 2 compliance with TeamPassword
Achieving and maintaining SOC 2 compliance requires a robust password management strategy. TeamPassword is your ultimate solution. By centralizing password storage and management, we provide a secure, efficient, and compliant approach to safeguarding your sensitive data.
Key Features for Your SOC 2 Toolkit:
-
Enforceable 2FA & Integrated TOTP: Mandate and simplify two-factor authentication, a cornerstone of SOC 2's security principle, to prevent unauthorized access.
-
Detailed Activity Logs: Maintain a clear, immutable record of all password activity. Provide auditors with the evidence they need to verify your security posture and accountability.
-
Granular Access Control: Implement the principle of least privilege with multiple user roles. Ensure team members can only access the credentials essential for their jobs.
-
Secure, Centralized Management: Eliminate risky password sharing and strengthen your overall security with a single, encrypted vault for all team credentials.
Ready to fortify your password defenses and simplify SOC 2 compliance? Try TeamPassword FREE for 14 days to understand how easy secure password management can be.
Enhance your password security
The best software to generate and have your passwords managed correctly.