What are Magic Links | A Guide to Passwordless Login
Have you ever wished you could log in to your favorite websites without having to remember or type a password? One way to make this happen is through magic links. Magic links are a simple way to authenticate users with just their email address.
Table of Contents
What are Magic Links?
Magic links are a way to sign into an account without a password. The process is similar to what happens when you click Forgot Password.
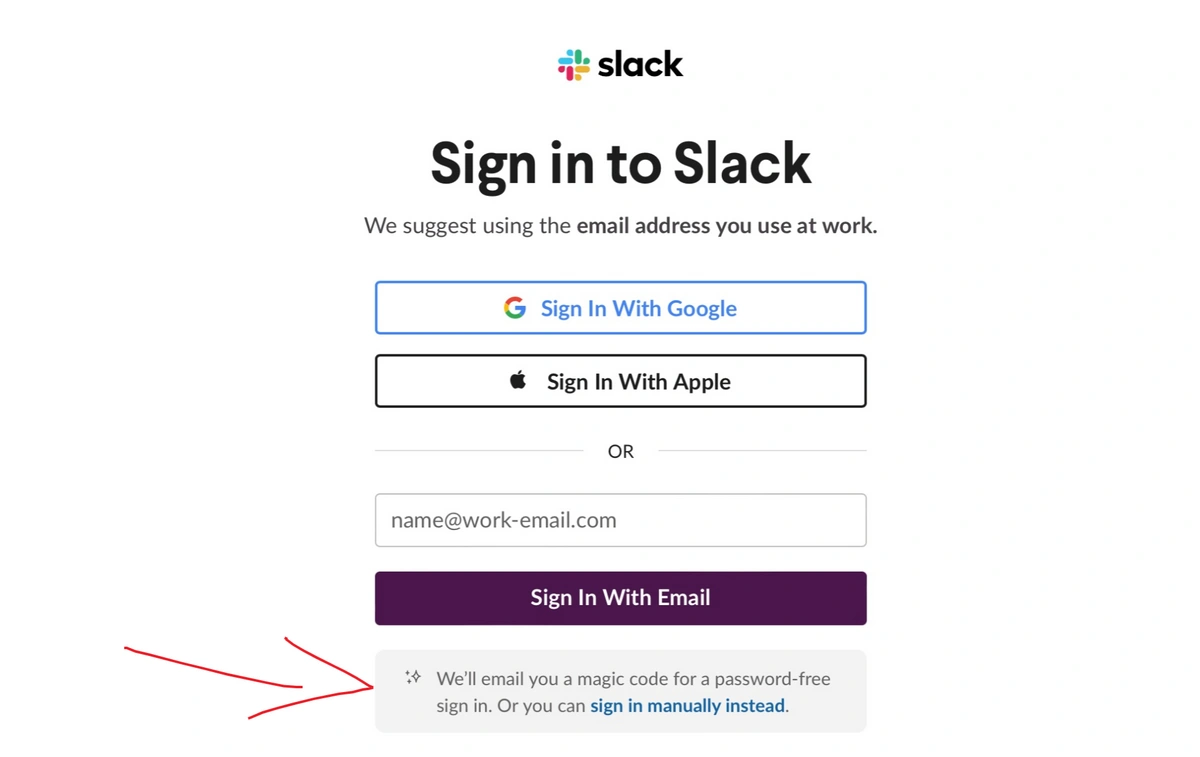
- Enter your email address in the sign-in form
- Click Sign-in with Email (or Send Magic Link - wording varies)
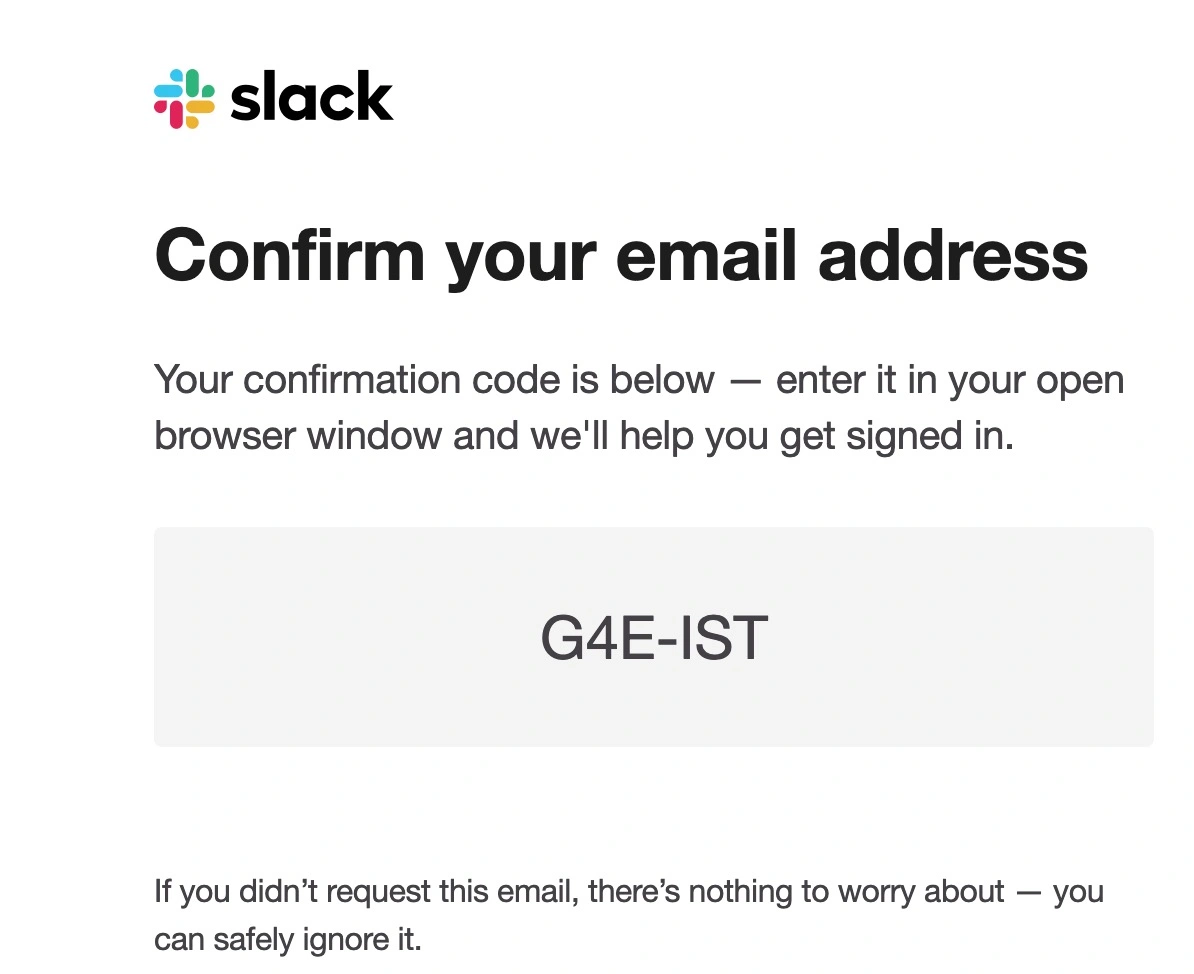
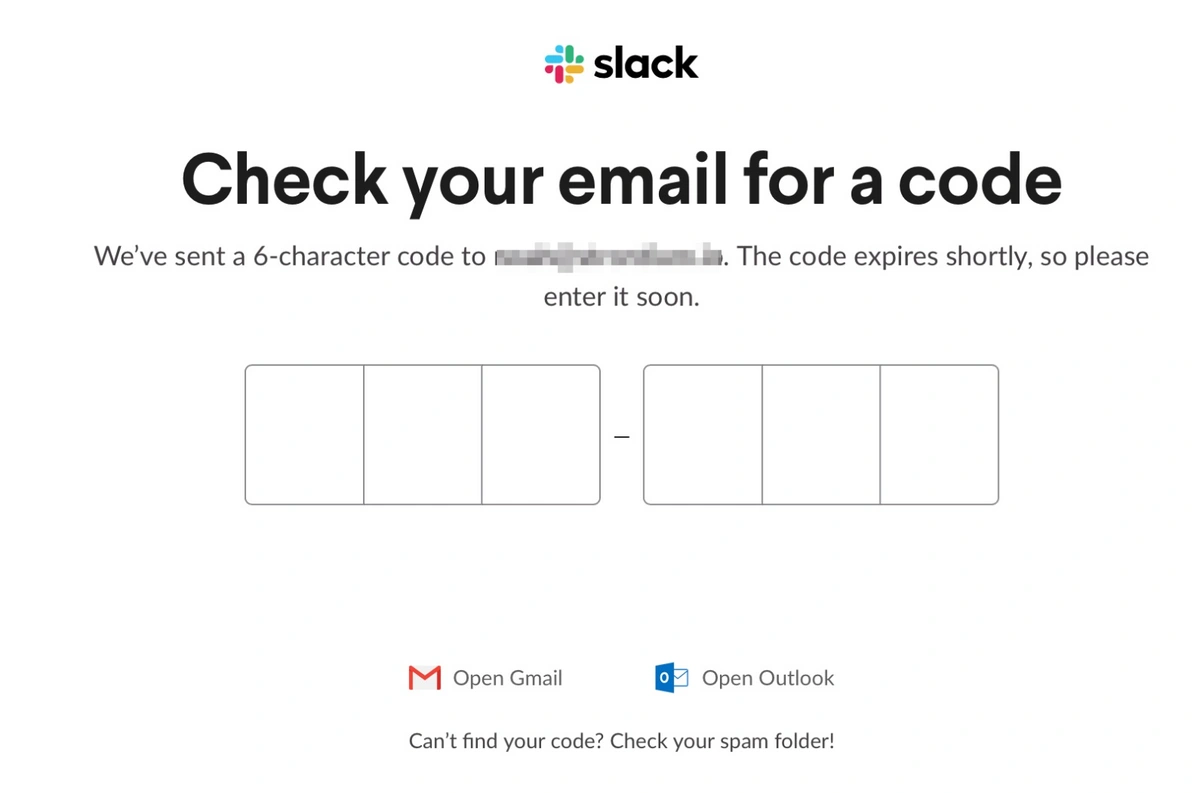
- Check your email, and click the link or enter the code to sign in
You’re now signed in! Links are for one-time use and typically expire after a certain amount of time. In the case of magic codes, such as what Slack uses in the example below, the code only works for the browser session that sent the request. If you close that window and go to sign in again, it will send you a new code.
Slack is one of the leading platforms that adopted magic links (or codes).
Why would a company have its customers use magic links instead of passwords to sign in?
You probably have over 100 online accounts. You’ve been told they should each have a unique, complex password. Without a password manager, however, it’s impossible to create secure passwords for every online service.
Given how many free and easy-to-use password managers are out there, there’s no excuse not to use one. But developers can’t force their customers to download password managers and practice good password hygiene.
That’s where magic links come in.
The goal is to make customers’ bad password habits a non-issue and eliminate frustrating “forgot password” experiences along the way.
Do magic links succeed?
Are magic links better than passwords?
While magic links have become more popular, they are far from being universally adopted. Let’s examine some pros and cons of magic links.
Pros:
- The customer doesn’t have to manage a password. That means no trying until you get locked out, no need to change it every 90 days, no password resets, and no getting hacked because you used that one password you use on every other account.
- Easier troubleshooting for support. If the user didn’t get their magic link by email, they either entered the wrong email, or the magic link went to spam (or was blocked entirely). In any case, support won’t have to listen to claims that “the correct password isn’t working.”
- Only relies on the customer having a properly secured email. Many people reuse passwords, and you can’t force them to use a password manager or generator. A time-bound, one-time-use link negates the danger of credential stuffing attacks, whereby a cybercriminal uses one password on a bunch of accounts in the hopes that it will unlock multiple things. It also eliminates the danger of phishing attacks where the criminal tricks the victim into giving up an essential piece of information.
Cons:
- An inverse to the above “pro”: magic links are only as secure as the user’s email. If a cybercriminal manages to hack the customer’s email, it’s over. Customers should use two-factor authentication, a strong, unique password, and ensure they know what devices have access to their email and where those devices are.
- Relies on the security of the network. If the customer uses unsecured wifi, a cybercriminal can use a man-in-the-middle attack to intercept the session token.
- Frustrating experience if things go wrong. The magic link could go to spam or take minutes to show up. If you’re logging in on a device where your email isn’t signed in, you’ll have to go do that - which might mean needing your phone for 2FA.
- Just like with passwords, admins cannot control who the link or code is shared with, or how.
Are magic links secure?
Like with every security measure, its effectiveness depends on how it’s used. While magic links eliminate specific cybersecurity issues intrinsic to passwords (such as phishing and credential stuffing attacks), they shift the burden of security to the customer’s email. And the security of your email is closely tied to your password hygiene, so a magic link won’t save you if you don’t practice good password habits. Anyone using magic links should:
- Use a secure email provider and enable 2FA.
- Check activity logs to make sure only recognized devices have access to your email and make sure you’re notified when new devices sign in.
- Only use encrypted networks.
On the positive side, no stolen password from another account will get a cybercriminal past the magic link (unless they’ve hacked your email), and there’s no point in them trying to phish your password away (unless they phish your email password).
Magic link security is also dependent on how it is set up. Here are some ways a developer can program their magic links to increase the security of the sign-in process:
- Magic links or codes only work once (this is pretty standard)
- Links and codes expire after a short amount of time
- The link must be opened on the same browser where it was requested
Some of these features come at the cost of potential friction in the user experience. What if the customer’s magic link email doesn’t arrive instantly? What if their email is signed in on a different computer than the one they’re trying to use the application on? Security and ease of use are in constant tension.
Magic Link Alternatives
Single Sign-On (SSO)
Single sign-on (SSO) is a system that allows users to log in to multiple applications or websites with one set of credentials. Users only need to authenticate once with a trusted identity provider, and then they can access all the services that are connected to the SSO system. SSO can simplify user management, reduce password fatigue, and enhance security.
Passwords + Multi-factor Authentication (MFA or 2FA)
While several prominent companies have adopted magic links over passwords, most online accounts still require a password.
Multi-factor authentication (MFA) is a technique that requires users to provide two or more pieces of evidence to prove their identity. The evidence can be something the user knows (such as a password or a PIN), something the user has (such as a phone or a token), or something the user is (such as a fingerprint or a face scan). MFA can increase the level of security and prevent unauthorized access.
Storing your login credentials in a password manager minimizes damage in the event that your email gets breached. People who don’t use a password manager are tempted to reuse passwords or store them in an excel or Google spreadsheet. Don’t put all your eggs in one basket.
There are free options out there if you need a password manager for personal use. If you need something for your business, TeamPassword is one of the best. If using password best practices is too hard, neither you nor your team will do it. TeamPassword makes it easy to store, update, and share credentials without them leaving an encrypted environment.
Fix Frustrating Password Predicaments with TeamPassword
Magic links aim to remove the frustration of being forced to create complex passwords you’re sure to forget. Magic links also eliminate the risk of certain cyberattacks and reused passwords, but remain at the mercy of the user’s email security. If your website or application requires high security, magic links probably aren’t a good choice. But if you want to streamline your customer’s login experience and minimize “forgot password” frustration, magic links can help you get there.
No one wants to check their email and click a link or paste a code each time they sign into an account. Passkey technology aims to provide a universally convenient solution in the future, but for now passkey adoption is limited; passwords remain a simple and relatively effective technology, albeit "outdated".
TeamPassword makes password sharing, storing, and filling easy and secure.
- AES 256-bit vault encryption
- Enforceable multi-factor authentication for your team
- Activity logs to see how your passwords are being used
- Unlimited groups and group-based sharing for PoLP best practices
- Incredibly competitive pricing
Enhance your password security
The best software to generate and have your passwords managed correctly.