Practical Guide to Man-in-the-Middle Attacks (and How to Stop Them)
Imagine you sent a private letter, but on its way, a rogue mailman opened it, read it, maybe even changed a few words, and then resealed it and delivered it. You and the recipient would never know your conversation had been compromised.
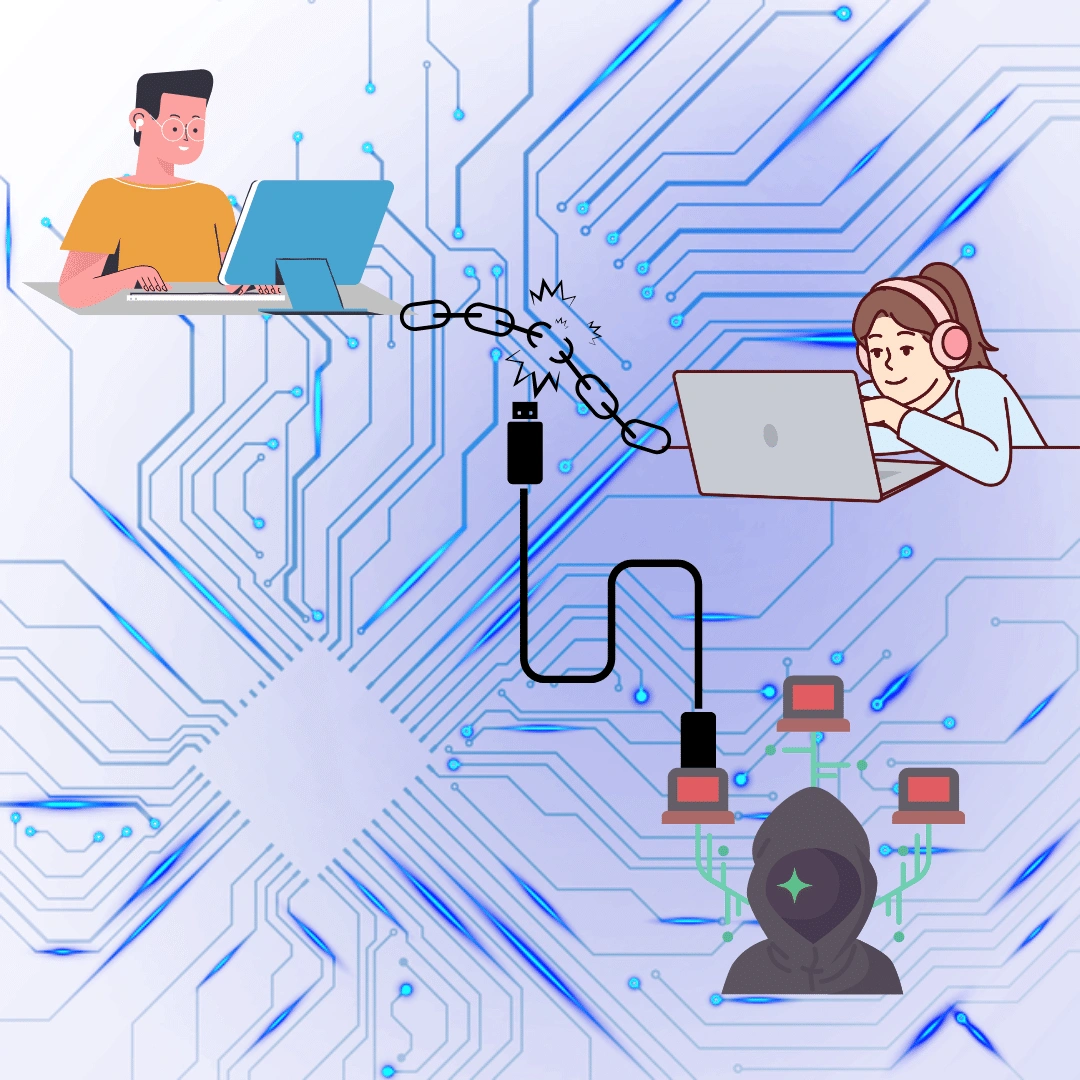
That’s exactly what a Man-in-the-Middle (MITM) attack is in the digital world. A cybercriminal secretly places themselves in the "middle" of your connection to an online service—like your bank, email, or a shopping site—to steal your passwords, credit card numbers, and personal data.
These attacks are sneaky and difficult to spot once they're happening. The good news? Preventing them is straightforward. This guide will walk you through five practical steps to secure your connection and keep your digital conversations private.
Table of Contents
What is a Man-in-the-middle attack?
A Man-in-the-middle attack is a type of cyberattack where an attacker intercepts and alters the communication between two parties who believe they are directly communicating with each other. The attacker can eavesdrop on, modify, or redirect the data that is being exchanged, without the knowledge or consent of the original parties.
How Do Man-in-the-Middle Attacks Actually Happen?
Circumventing the complex code and jargon, here's how "MITM" attacks happen in everyday situations. The goal is always to trick you or your device into connecting to the attacker instead of the real destination.
Here are a few common ways they do it:
-
"Evil Twin" Public Wi-Fi: An attacker sets up a fake Wi-Fi network with a convincing name, like "CoffeeShop_Free_WiFi" or "Airport_Guest." When you connect, all your internet traffic goes through their computer first, allowing them to see everything you do.
-
Phishing Emails or Links: You might get an email that looks like it's from your bank, asking you to "verify your account." The link leads to a fake website that looks identical to the real one. When you enter your password, the attacker captures it and then redirects you to the real site, making it seem like you just had a login error.
In both cases, the attacker becomes an invisible eavesdropper on your connection.
5 Practical Ways to Prevent MITM Attacks
The good news is that there are some effective ways to protect yourself from MITM attacks and ensure your online security and privacy. Here are some of the best practices that you should follow:
1. Secure Your Home and Personal Wi-Fi
Your home network is the foundation of your online security. Leaving it unprotected is like leaving your front door unlocked.
-
What to do:
-
Ensure your Wi-Fi is protected with the latest security protocol, ideally WPA3 (or WPA2 at a minimum). You can find this setting in your router's administration pane. To access this setting, log in to your router's web interface by entering its IP address - often 192.168.0.1 or 192.168.1.1 - into your browser's address bar and navigating to the administrative or advanced configuration menu.
-
Change your router's default administrator username and password. Cybercriminals have public lists of these default credentials.
-
-
Why it works: Strong encryption scrambles all the data traveling over your Wi-Fi, making it gibberish to anyone trying to eavesdrop. A unique router password prevents an attacker from taking control of your entire network.
-
Pro-Tip: Make your router's password a long but memorable passphrase.
2. Use a VPN, Especially on Public Wi-Fi
The best security measure is to use your personal hotspot instead of public Wi-Fi. But if you are in a situation where you must connect to a public network, use a reputable VPN service.
A Virtual Private Network (VPN) is your best friend when you're using a network you don't control.
-
What to do: Before you start browsing at a hotel, airport, or coffee shop, turn on a reputable VPN service on your laptop or phone.
-
Why it works: A VPN creates a secure, encrypted "tunnel" for your internet traffic. Even if you're on a compromised network, the attacker in the middle can't see what you're doing. All they can see is scrambled, unreadable data. It's like sending your mail through a locked, armored truck instead of a transparent envelope.
-
Pro-Tip: Choose a well-known, paid VPN provider with a strict "no-logs" policy. This ensures they aren't keeping records of your online activity.
3. Always Look for the Lock (HTTPS)
That little padlock icon next to the website address in your browser is more important than you think.
-
What to do: Always check for a padlock icon and an address that starts with
https://before entering any sensitive information on a website. If you see a "Not Secure" warning, do not proceed. -
Why it works: The "S" in HTTPS stands for "Secure." It means your connection to that website is encrypted and authenticated. This verifies you're connected to the real server, not an imposter, and prevents anyone in the middle from reading the data you exchange.
-
Pro-Tip: Most modern browsers, like Chrome and Firefox, have a setting to automatically warn you or try to upgrade your connection to HTTPS. You can usually find it under
Settings > Privacy and Security.
4. Keep Your Devices and Apps Updated
Those constant "update available" notifications can be annoying, but they are crucial for your security.
-
What to do: Enable automatic updates on your computer, phone, and web browser. Don't ignore manual update prompts for your apps.
-
Why it works: Hackers find and exploit security flaws, or "vulnerabilities," in outdated software to insert themselves into your connection. Software updates almost always include patches that fix these vulnerabilities, shutting the door on attackers.
-
Pro-Tip: If you have software you no longer use, uninstall it. An old, forgotten app is an unpatched security risk.
5. Be Skeptical of Unsolicited Links and Pop-ups
Attackers often don't need to break through digital walls when they can just trick you into opening the door for them.
-
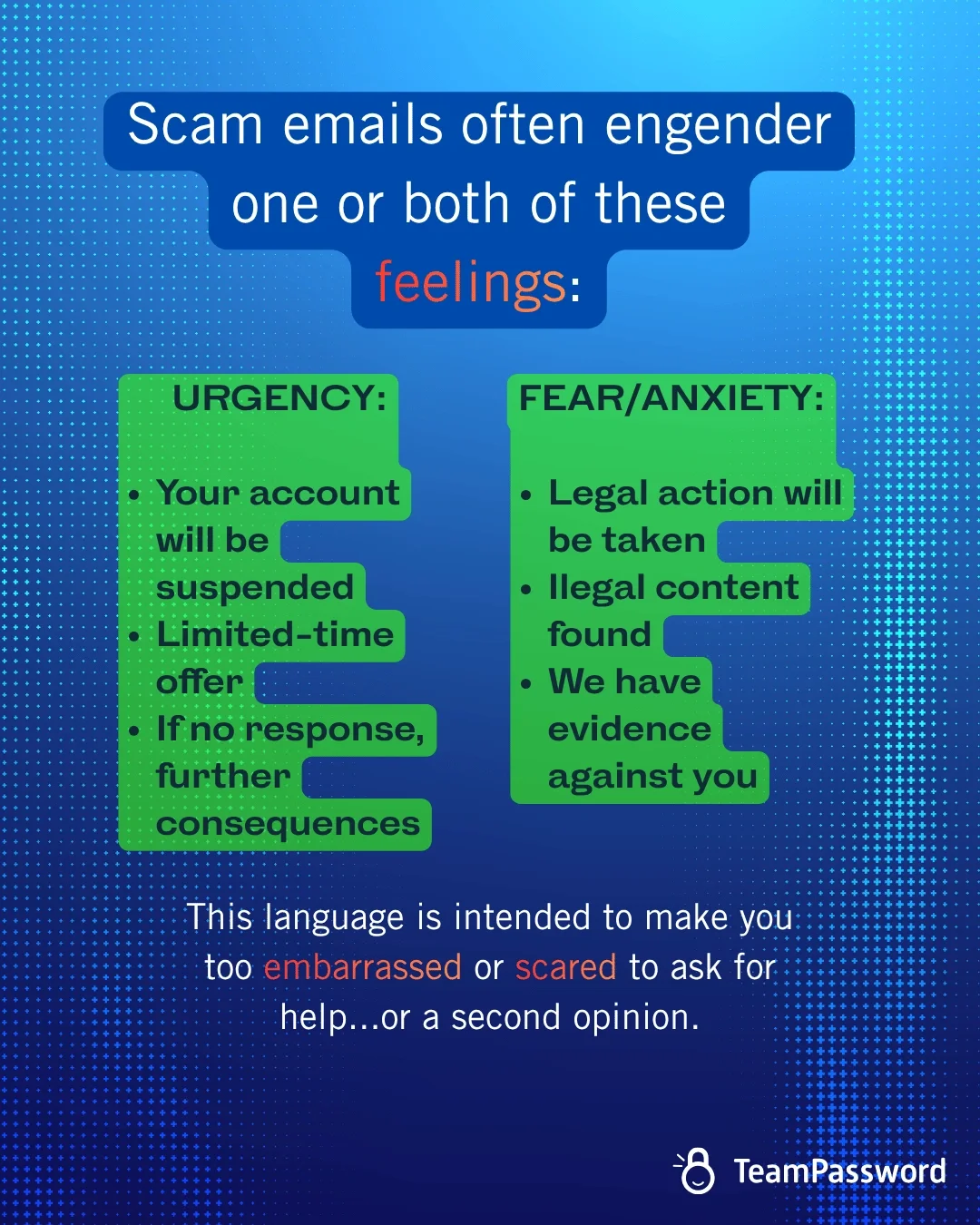
What to do: Treat unexpected emails, text messages, and social media DMs with suspicion. Be especially wary of messages that create a sense of urgency, like "Your account has been suspended, click here IMMEDIATELY." Scam emails typically engender two feelings: Urgency (I have limited time to take action before something bad will happen) and Fear/anxiety (I've made a mistake, and am too embarrassed to tell anyone or ask for help).
-
Why it works: This is the human element of security. By pausing and thinking before you click, you can avoid the fake websites and malicious links that are the starting point for many MITM attacks.
-
Pro-Tip: If you get an urgent message from a service like your bank, close it. Then, open your browser and type the bank's website address in manually to log in and check for any real alerts.
Using TeamPassword to minimize MITM attacks
The primary goal of many MITM attacks is to steal your credentials. If an attacker gets the password to your email, they can reset the passwords for almost all your other accounts.
This is why password security is so critical. Using the same simple password everywhere is a recipe for disaster. But how can you possibly share passwords with your family or work team securely? Emailing them or writing them in a shared document is just as risky as using an unsecured Wi-Fi network.
TeamPassword is a secure password manager built for frictionless sharing. TeamPassword uses industry-standard AES 256-bit encryption to secure your passwords in a vault only you can unlock. Use unlimited password groups to distribute access. Turn on the one-time-share feature to securely share credentials - the link will be automatically destroyed after opening.
Password hygiene needs to be so easy that your team will actually do it. Otherwise, people revert to easy, insecure habits like spreadsheets and emails, which results in passwords not being accounted for.
Don't take our word for it. Try TeamPassword for free to transform password security for your company.
FAQs
What tool can be used to prevent man in the middle attacks?
Virtual Private Networks (VPNs) create an encrypted tunnel between your device and a remote server.
This prevents eavesdroppers (including potential MITM attackers) from intercepting your data. However, keep in mind that not all VPNs are equally secure; choose reputable providers, and understand that your VPN provider is the man-in-the-middle.
The best tool against MITM attacks is a secure connection you can verify and control.
Does a VPN protect against man in the middle attacks?
Yes, if you trust the VPN.
Essentially, the VPN provider is the man in the middle. If the encryption on your tunnel is solid, then you should be protected against packet sniffing between your endpoint and the VPN provider.
When does a VPN not protect against MITM attacks?
VPNs do not improve your endpoint security. Therefore, VPNs do not help in the following situations:
-
Non-encrypted connections
- Non-encrypted connections are internet connections where data is transmitted without encryption, meaning the information is sent in plain text. This makes it vulnerable to interception by attackers, who can easily read or manipulate the data without any need for decryption.
-
DNS poisoning
- DNS poisoning, also known as DNS spoofing, is a cyberattack where a hacker alters the domain name system (DNS) records to redirect users to malicious websites. This can trick users into providing sensitive information like login credentials or personal data, under the guise of legitimate sites.
-
Software vulnerabilities
- Software vulnerabilities refer to weaknesses or flaws in a software program that can be exploited by cybercriminals to gain unauthorized access, install malware, or steal data. These vulnerabilities often arise from coding errors, outdated software, or unpatched security issues.
If there are local issues with the WiFi, or malware on your device or browser already, then a VPN won't save you.
Can you detect a MITM attack?
When you use HTTP, you can't tell if someone is intercepting your data. But when you use HTTPS, your browser can detect and alert you about it. Exceptions are if your device or the server you're connecting to (or the certificate authority that vouches for it) is already hacked.
Detecting an MITM attack involves vigilance and understanding common signs. Here are some indicators:
- Certificate Warnings:
- When accessing a website, your browser checks its SSL/TLS certificate.
- If the certificate is invalid or doesn’t match the domain, you’ll receive a warning.
- Pay attention to such warnings, especially if you’re not expecting them.
- Unexpected Redirects:
- If a website unexpectedly redirects you to a different domain, it could be a sign of tampering.
- Verify the URL and ensure it matches the site you intended to visit.
- Unusual Behavior:
- Unexpected changes in website behavior (e.g., altered content, missing elements) may indicate an attack.
- Compare with previous visits to identify anomalies.
- Network Monitoring Tools:
- Use network monitoring tools to inspect traffic.
- Look for unusual patterns, unexpected connections, or suspicious IP addresses.
- Check SSL/TLS Details:
- Inspect SSL/TLS details (such as cipher suites) during a connection.
- Mismatched or weak encryption can signal an issue.
-
Verify Public Keys:
- When using public key cryptography (e.g., RSA), verify the authenticity of public keys.
- Manually compare fingerprints or use trusted channels to share keys.
Prevention is the best defense against MITM attacks. MITM is intended to be transparent to the victim. Follow the steps in the article to prevent becoming a victim.
Enhance your password security
The best software to generate and have your passwords managed correctly.