6 Steps to Using a Password Manager for your Small Business
For small businesses, efficient and secure password management is crucial. This guide to using a password manager for small business will walk you through the essential steps to set up a password manager effectively. Learn how to use a password manager for your small business to streamline operations, enhance security, and get back to focusing on what you do best.
Table of Contents
6 steps to set up your small business password manager for success
1. Define User Access Needs: The First Step in Setting Up Your Password Manager
Before you even configure your chosen password manager, you need a clear picture of who needs access to what. Your employees will require access to specific accounts, and often, external vendors or consultants will too. For instance, does your bookkeeper need credentials for your credit card portal? Does your marketing consultant require access to your company's Twitter account? Compile a comprehensive list of every individual who will need password access. This initial inventory is foundational for setting up your password manager correctly.
2. Create Role-Based Groups in Your Password Manager
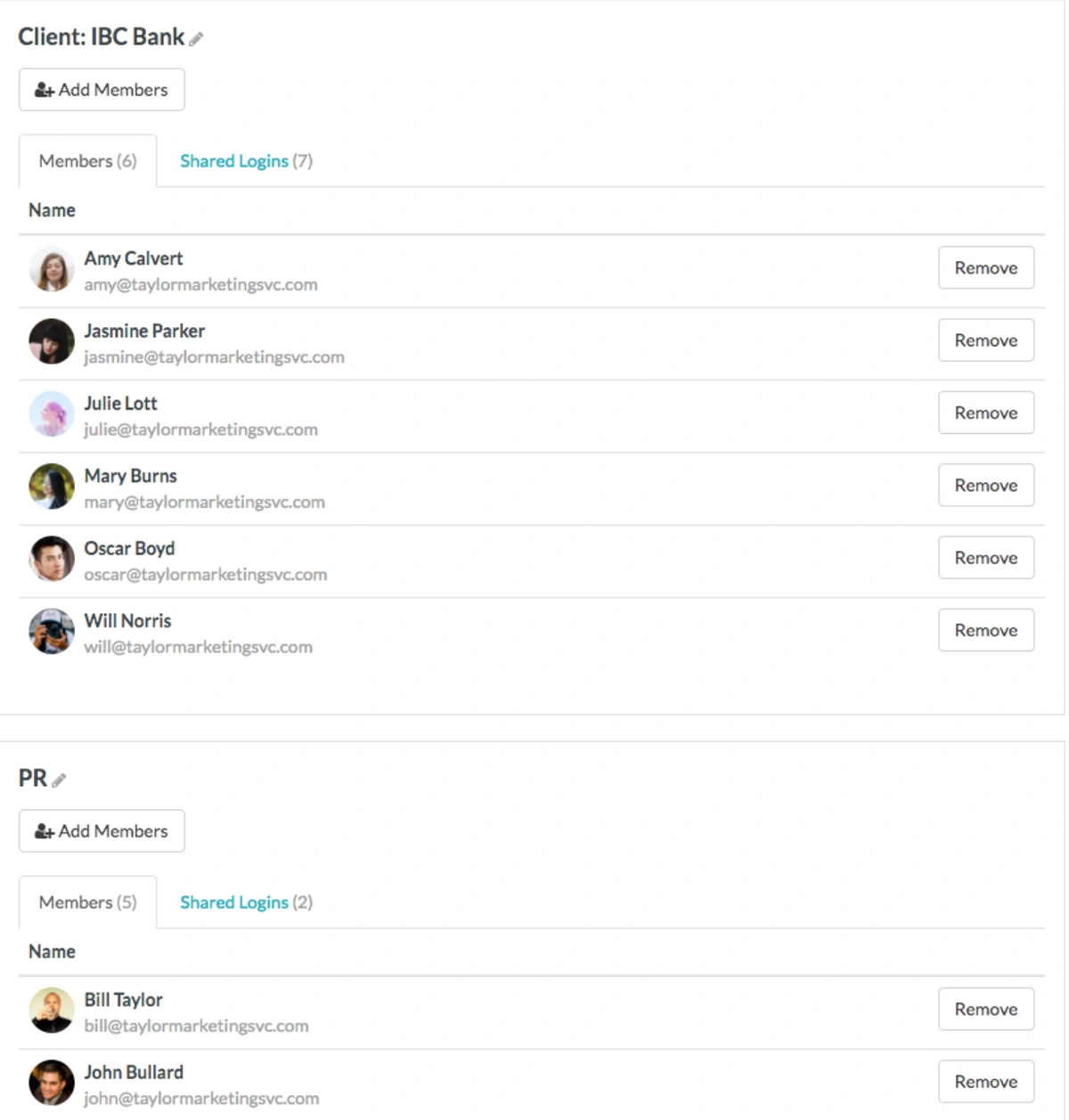
Once you've identified everyone needing access, the next step in how to use a password manager for your small business effectively is to organize these individuals into distinct password access groups within the manager itself. For example, your technical team probably doesn't need the login details for your accounting software, and your marketing team likely won't require access to HR platforms. Here are some common groups we see small businesses implement when they set up a password manager:
- Administrative: Office managers and administrative staff often need access to accounts like office supply vendors (e.g., Staples), general purchasing accounts (e.g., Amazon), and travel booking sites for hotels and airlines.
- Finance: Bookkeepers, accountants, and anyone handling financial operations will need access to critical accounts such as your commercial bank, credit cards, and payroll system.
- Marketing: Your internal marketing team, external consultants, or digital agency will require access to social media platforms (Twitter, Facebook), marketing automation tools (Hootsuite, Mailchimp), domain registrars (GoDaddy), and any Content Management Systems (CMS) your business or clients use.
Creating these groups in a dedicated tool like TeamPassword is straightforward. It ensures that the appropriate people—and only the appropriate people—have access to the passwords they genuinely need for their roles.
3. Integrate Password Manager Access into Your Hiring Procedures
You likely already have procedures for new hires, such as collecting tax information and setting them up in payroll. We strongly suggest adding one more vital step: add the new employee to their designated password groups within your password management application. This ensures that new team members are never delayed or unable to perform their duties because they're waiting for someone to share a necessary password.
4. Secure Your Business: Update Termination Procedures in Your Password Manager
While no one enjoys planning for an employee's departure, it's a realistic and essential aspect of business operations. Preparing for when someone leaves (whether voluntarily or not) is vital for security. You absolutely do not want a disgruntled former employee to retain access to your bank accounts, social media profiles, or other sensitive company information.
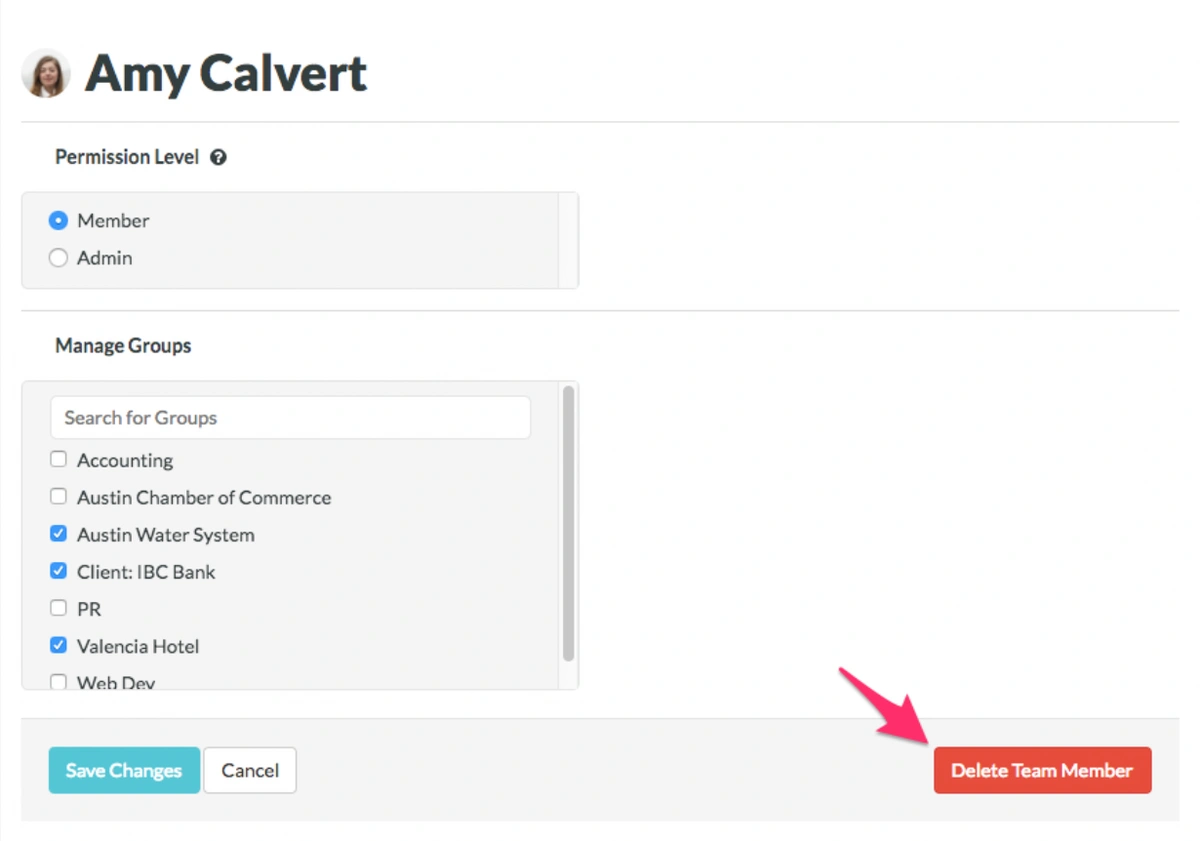
To minimize risk, even if an employee leaves on good terms, you must promptly remove them from your password manager (e.g., their TeamPassword account). Poor personal password habits of an ex-employee could inadvertently jeopardize your company's security. If one of their personal accounts linked to old company access gets hacked, your business's password security—and by extension, its financial accounts, credit cards, and reputation—could be significantly endangered.
5. Don't Overlook Consultants and Vendors in Your Password Manager Setup
Your guide to using a password manager for small business wouldn't be complete without addressing third-party access. When you engage with external consultants or vendors, ensure they are added to specifically designated, limited-access groups within your password manager. Crucially, just as with an employee termination, if you cease working with a consultant or vendor, you must immediately revoke their access to your company passwords.
6. Regularly Audit Password Access Within Your Manager
Humans make mistakes; it's inevitable. That's why ongoing vigilance is key to keeping your small business secure. Establish a regular schedule—perhaps quarterly—to log in and thoroughly review your password groups and user access.
First, confirm that all users in your password manager are current employees or active vendors.
Second, meticulously check the group assignments for each user. For example, if an employee transitioned from an administrative role to a marketing position, they might no longer require access to the company's Amazon purchasing account. These regular check-ins also serve as a failsafe to ensure, for instance, that a tech intern wasn't accidentally granted access to all your banking credentials.
Stop risking your small business's security with insecure shared documents and outdated spreadsheets.
TeamPassword was built to help you take control and implement strong password management practices, easily.
With TeamPassword, you can:
- Keep costs low with affordable pricing designed for small businesses.
- Boost your security with enforceable Two-Factor Authentication (2FA).
- Simplify logins using our integrated TOTP authenticator.
- Organize everything with unlimited records and groups for all your team's passwords.
- Maintain oversight with comprehensive activity logs.
By setting up TeamPassword and consistently using it, you can finally say goodbye to password chaos and the constant threat of security breaches.
Ready to take control? Give TeamPassword a try with our free 14-day trial!
Enhance your password security
The best software to generate and have your passwords managed correctly.