How to Make a Strong Password (and Keep it Secure)
In a world of endless online accounts, the pressure to create and remember countless passwords can feel overwhelming. You know "password123" is a terrible choice, but is Tr0ub4dor&3 really that much better? It’s hard to remember, a pain to type, and as you'll soon learn, not nearly as secure as you might think.
The good news is that modern password security has gotten much simpler. It’s no longer about memorizing impossible strings of random characters. It’s about adopting a smarter strategy. This practical guide will walk you through the current best practices for creating and managing passwords that are both incredibly strong and easy to handle.
Key Takeaways for Strong Passwords:
- Length is King: A long password (16+ characters) is exponentially more secure than a short, complex one.
- Use Passphrases: Memorable, multi-word phrases are the easiest way to create long, secure passwords that you can actually recall.
- Never Reuse Passwords: Every account needs a unique password. A single reused password can compromise your entire digital life.
- Use a Password Manager: This is the only practical way to follow these rules. It securely stores and fills your passwords for you.
- Enable MFA (2FA): Multi-factor authentication is your ultimate safety net, protecting you even if your password is stolen.
Table of Contents
The 4 Rules for a Strong Password in 2025
Forget everything you thought you knew about adding symbols and numbers to short words. Modern password security, endorsed by experts and institutions like NIST, is built on these four simple, powerful rules.
Rule #1: Prioritize Length with Passphrases
For years, users were told to create complex but short passwords. We now know this is outdated advice. A short, complex password like P@$$w0rd! is hard for a human to remember but trivial for a modern computer to crack.
The new gold standard is the passphrase: a sequence of four or more random words.
A passphrase like Vivid-Purple-Whale-Calendar is incredibly easy for you to remember but would take a computer centuries to guess. It achieves its strength through sheer length, which is the single most important factor in password security.
Rule #2: Never Reuse Passwords
Using the same password for multiple accounts is like using the same key for your house, car, and office. Once a criminal gets that one key, everything you own is unlocked.
Data breaches happen daily. When a service like LinkedIn or Adobe gets hacked, lists of emails and passwords are leaked and sold online. Attackers then take these lists and automatically try them on other high-value sites like your bank, email, and company accounts—a technique called "credential stuffing." If you reuse passwords, a breach on a low-security forum can lead to your entire digital identity being compromised.
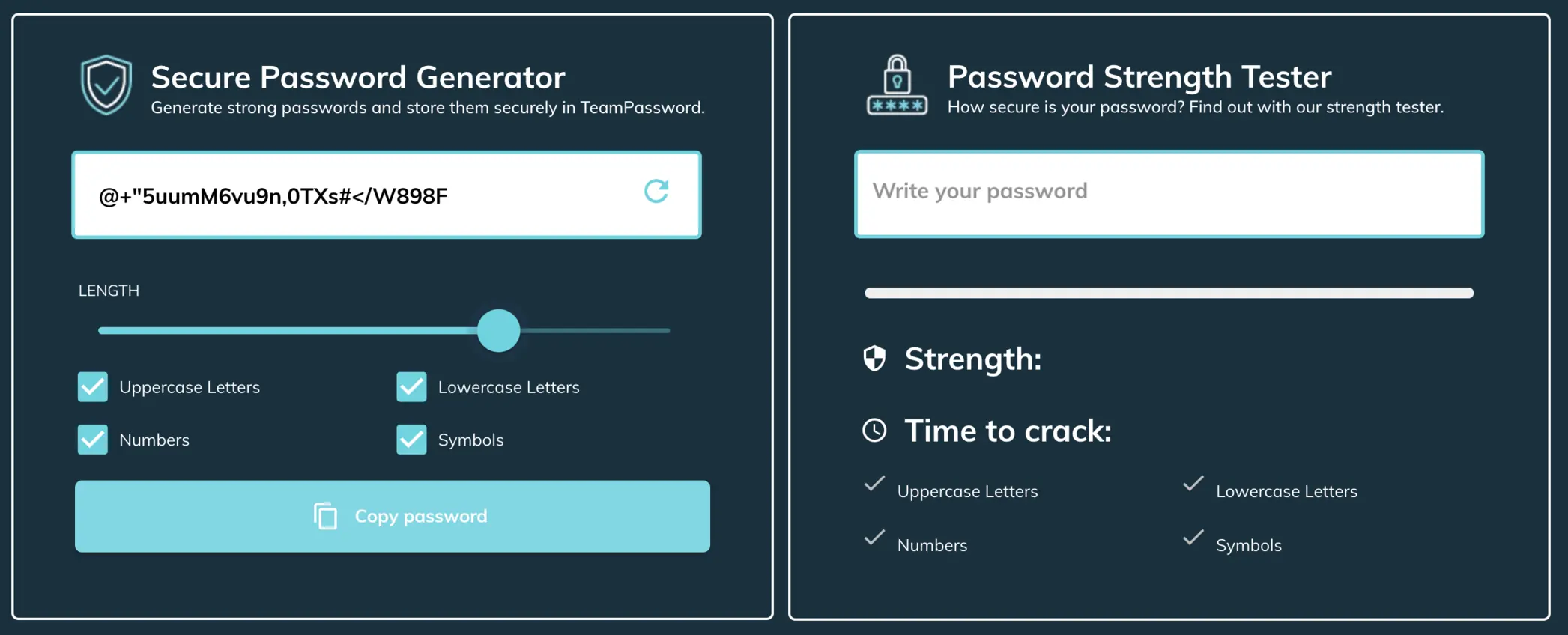
A password generator is a useful tool in achieving unique, secure passwords when combined with a password manager.
Rule #3: Use a Password Manager
Following the first two rules—creating long, unique passphrases for every single account—is impossible without help. This is where a password manager becomes an essential tool.
A password manager is a secure, encrypted vault that does the heavy lifting for you:
-
It generates long, random, and secure passwords with a single click.
-
It saves and stores them securely in your encrypted vault.
-
It automatically fills them in when you log into your accounts.
For businesses, a team-focused password manager like TeamPassword is crucial. It allows you to securely share access to company accounts without ever exposing the underlying password, ensuring your team can work efficiently without resorting to insecure methods like spreadsheets or chat messages.
Rule #4: Always Use Multi-Factor Authentication (MFA)
Think of your password as the lock on your front door. Multi-Factor Authentication (also called Two-Factor Authentication or 2FA) is the security system, the deadbolt, and the guard dog all in one.
MFA requires a second piece of information to log in—usually a temporary code from an app on your phone. Even if a criminal manages to steal your password, they can't get into your account because they don't have your second factor. Whenever possible, use an app-based authenticator (like Google Authenticator, Ente Auth, or your password manager's built-in authenticator) as it is far more secure than codes sent via SMS text message.
TeamPassword provides a couple of relevant features:
- Integrated TOTP Authenticator so that time-based 2FA codes are generated within TeamPassword, enabling shared accounts with 2FA protection to be easily accessible by your team
- Enforceable 2FA: Requires all users on your TeamPassword organization to enable 2FA for their account
Strong Password Examples: Good vs. Bad
Visualizing the difference makes it clear why passphrases are the modern standard.
| Password Type | Example | Why It's Bad / Good |
| Weak & Common | qwert123 |
Top of every hacker's list. Cracked instantly. |
| Predictable Substitution | P@$$w0rd! |
Looks complex, but uses common substitutions (a>@, o>0) that cracking tools check first. Deceptively weak. |
| Good Passphrase | correct-horse-battery-staple |
Long (28 characters), easy to remember, and contains enormous randomness for a computer to guess. Incredibly strong. |
| Excellent Passphrase | Vivid!Purpl3-Whale-C@lendaR |
Combines the immense length of a passphrase with added complexity for maximum security in the most critical accounts. |
Common Password Mistakes You Must Avoid
-
Reusing Passwords: As mentioned, this is the cardinal sin of password security. A breach on one site will lead to others being compromised.
-
Using Personal Information: Avoid using names, birthdays, anniversaries, pets' names, or street addresses. This information is often publicly available.
-
Using Known-Compromised Passwords: Before using a password, you can check it against a database of known-leaked credentials at
haveibeenpwned.com/Passwords. -
Storing Passwords Insecurely: Never store passwords in spreadsheets, documents, emails, or on sticky notes. These methods lack encryption and are easily discovered.
Deeper Dive: The "Why" Behind Strong Passwords
For those curious about the mechanics, here’s a quick look at why these rules are so important.
Hackers use automated tools to guess passwords at incredible speeds—thousands or even millions of guesses per second. This is called a brute-force attack. The attacker's success depends on the password's "search space"—the total number of possible combinations.
-
Complexity's Flaw: A short, 8-character password using uppercase, lowercase, numbers, and symbols has a large search space, but it's still within the realm of possibility for a powerful computer to crack in hours or days.
-
Length's Power: Each character you add to a password increases the search space exponentially. Increasing a password's length from 8 to 16 characters doesn't just double its strength; it can make it billions of times stronger, pushing the cracking time from days to centuries. This is why a 28-character passphrase is so much more effective than an 8-character complex string.
When you use an online service, they should be using a secure hashing algorithm to store your password. This turns your password into a long, scrambled string of text. Slow, robust hashing algorithms make brute-force attacks much harder for criminals, but you have no control over which services use them properly. Therefore, the only thing you can control is the strength of the password you create in the first place.
Your Secure Path Forward
Creating strong, secure passwords in 2025 is no longer a memory test. It’s a strategy. By embracing long passphrases, using a unique one for every account, and protecting it all with a password manager and MFA, you build a formidable defense against cyberattacks.
Get robust security features that are simple to manage, including enforceable 2FA, detailed activity logs, and an integrated TOTP authenticator. Empower your team with unlimited records, flexible user-roles, and a seamless Google sign-in to get started in minutes.
Protect your entire business for a price that makes sense, with plans starting at just $2.41/user/month.
Enhance your password security
The best software to generate and have your passwords managed correctly.