What Is SIM Swapping and How to Prevent SIM Swap Attacks
Have you ever gotten a text message with a code you didn't request? Maybe it was for logging into your bank account or social media profile. If so, you might be a target for a SIM swapping scam.
In this blog post, we'll break down what SIM swapping is, how it works, and how you can protect yourself from this increasingly common threat.
Here are the key things you need to know about SIM swapping:
- SIM swapping is a scam where a thief takes control of your phone number by transferring it to a new SIM card.
- Social engineering and phishing are often used to trick your carrier into making the switch.
- Once they have control of your number, attackers can intercept your calls, texts, and two-factor authentication codes.
- There are steps you can take to protect yourself from SIM swapping, such as using strong passwords, enabling two-factor authentication on all your accounts, and being careful about what information you share online.
- If you think you've been a victim of SIM swapping, contact your carrier immediately.
Table of Contents
What Is SIM Swapping?
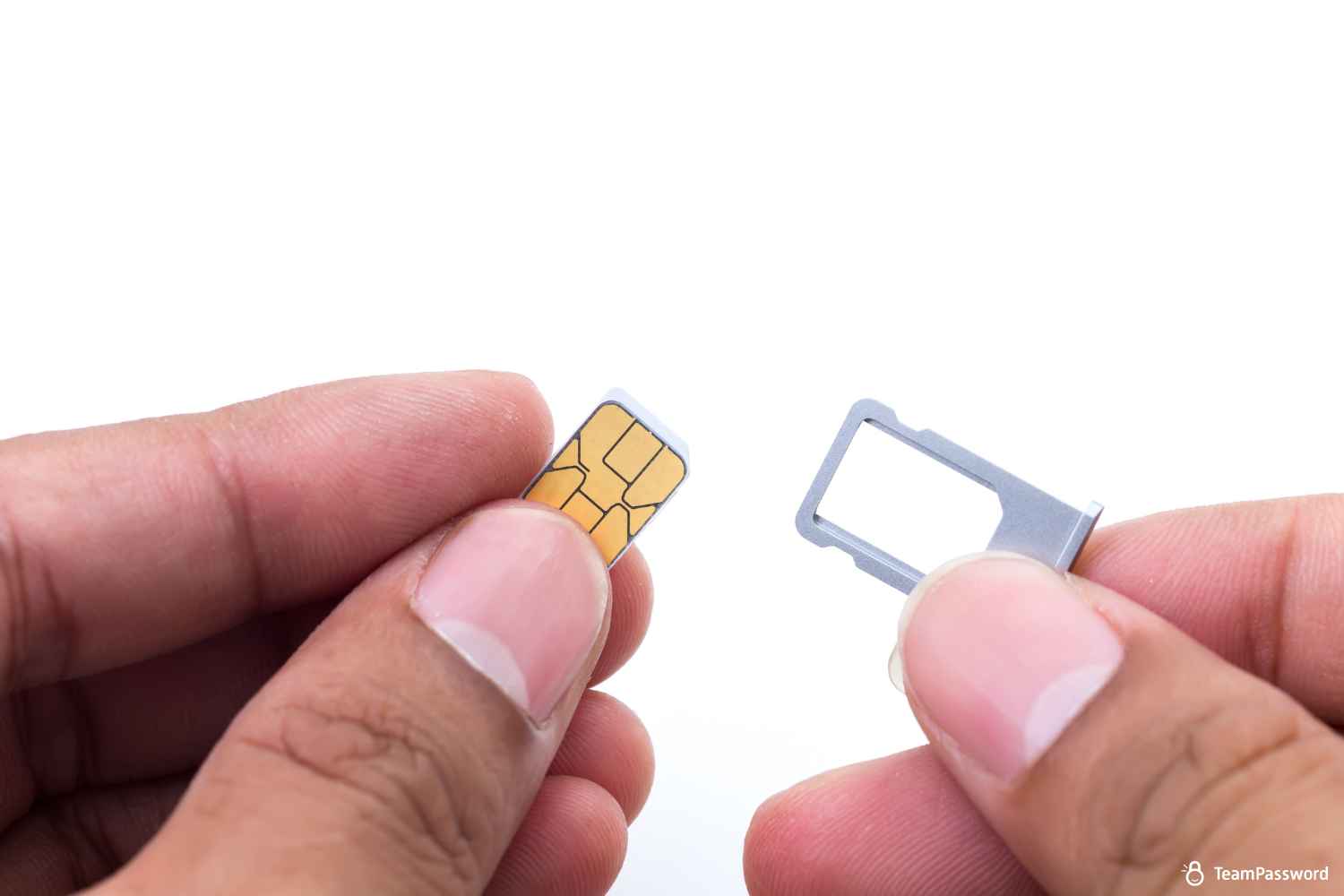
SIM swapping, also known as SIM jacking or port-out fraud, is a scam where a cybercriminal gains control of your phone number by transferring it to a new SIM card. This allows them to intercept your calls, texts, and two-factor authentication codes, which they can then use to access your online accounts, such as your bank account, email, or social media profiles.
SIM cards are tiny chips that store your phone number and other subscriber information. They allow your phone to connect to your carrier's network and make calls, send texts, and access data.
SIM swapping can be a very effective scam because it relies on social engineering, which is the art of tricking people into giving up personal information. Scammers will often use a variety of techniques to gather information about their victims, such as phishing emails, social media stalking, or even buying personal information on the black market.
Once they have enough information, the attacker will contact your carrier and pretend to be you. They will try to convince the carrier representative to transfer your phone number to a new SIM card that they have in their possession. In some cases, they may be successful, especially if they have been able to gather personal information about you, such as your birthday or the last four digits of your Social Security number.
How Does SIM Swapping Work?
SIM swapping scams typically involve a two-step process:
-
Information Gathering: The attacker will first try to gather as much personal information about you as possible. This information could include your name, address, date of birth, Social Security number, phone number, and the answers to your security questions. They may use a variety of techniques to gather this information, such as:
- Phishing scams: Phishing emails or text messages that appear to be from a legitimate source, such as your bank or phone company. These messages will often try to trick you into clicking on a link or entering your personal information into a fake website.
- Social media stalking: Attackers can glean a surprising amount of personal information from your social media profiles, such as your birthday, hometown, and the names of your friends and family.
- Buying information on the black market: Personal information is unfortunately readily available for purchase on the dark web.
-
Porting the Number: Once the attacker has enough information about you, they will contact your carrier and pretend to be you. They will try to convince the carrier representative to transfer your phone number to a new SIM card that they have in their possession. They may use the information they have gathered to answer your security questions or verify your identity.
If the attacker is successful, your phone number will be transferred to the new SIM card. This means that all of your calls, texts, and two-factor authentication codes will now be sent to the attacker's phone instead of yours. The attacker can then use this information to access your online accounts and steal your money or identity.
The Consequences of SIM Swapping: What’s at Stake?
SIM swapping can have severe consequences beyond just losing access to your phone number. Here are some of the risks victims face:
-
Financial Loss: With access to two-factor authentication codes sent to your phone, attackers can breach bank accounts, investment platforms, and financial apps, potentially draining accounts or making unauthorized purchases.
-
Identity Theft: Attackers can use access to your texts and calls to take over personal accounts, change account settings, and gather personal information that can be sold or used for further scams.
-
Data Breach in Professional Accounts: For business owners, freelancers, and professionals like accountants, a SIM swap can compromise sensitive client data if attackers gain access to business emails or work-related accounts. This could lead to legal consequences or reputation damage.
-
Loss of Access to Essential Services: Losing control of your phone number could mean being locked out of crucial online services, including social media, cloud storage, and communication tools, disrupting both personal and professional life.
How Do I Report a SIM Swap Attack?
If you think you've been a victim of SIM swapping, the most important thing to do is to contact your carrier immediately. The sooner you report the scam, the sooner they can take steps to prevent further damage.
Here's how to report a SIM swap, but keep in mind the specific instructions may vary depending on your carrier:
- Call your carrier's customer service number. You can usually find this number on your carrier's website or on your monthly bill.
- Explain to the customer service representative that you believe you've been a victim of SIM swapping.
- Provide the representative with as much information as possible, such as your name, account number, and the phone number that was swapped.
- The carrier will likely freeze your account and issue you a new SIM card.
- Once your account is secure, you should also change the passwords for all of your online accounts.
Here are some additional resources that you may find helpful:
- Verizon: https://www.verizon.com/about/account-security/sim-swapping
- AT&T: https://about.att.com/pages/cyberaware/ni/blog/sim_swap
- T-Mobile: https://www.t-mobile.com/support/business/change-sim-card
How to Protect Yourself from a SIM Swap
There are a number of steps you can take to protect yourself from SIM swapping:
1. Set a Security PIN or Port-Freeze with Your Carrier
This is your most powerful defense. Contact your mobile carrier (Verizon, AT&T, T-Mobile, etc.) and ask them to add a port validation PIN or a "port-freeze" to your account. This PIN, which only you should know, will be required before your number can be transferred to a new device or carrier. Without it, most SIM swap attempts will be stopped dead in their tracks.
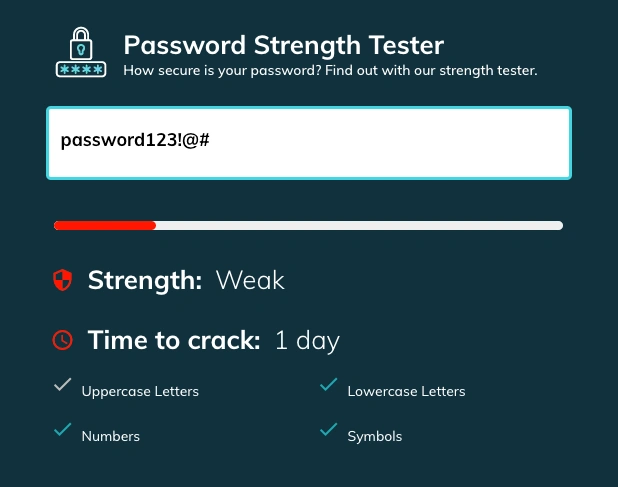
2. Always use Strong, Unique Passwords for Every Account
SIM swapping can be used for several nefarious schemes, but one of the most damaging is to capture your 2FA code. Unfortunately, many banks and other sensitive accounts allow or even require SMS-based multi-factor authentication. If your password is weak, the only thing that stands between a cyberthief and devastation is your phone carrier's (underpaid) customer support representative.
With a strong, unique password on every account, you at least mitigate the chance of a threat actor getting past step 1.
Use a password generator in combination with a password manager to make secure passwords easy.
Protecting your email is especially important since most password reset flows work on the assumption that your email is secure!
If you need to share login credentials or have employees whose habits could endanger your company, you may want to invest in an affordable, collaboration-first password manager like TeamPassword.
3. Avoid SMS 2FA When Possible
Two-factor authentication (2FA) is an extra layer of security that helps to protect your online accounts. When you enable 2FA, you're required to enter a code in addition to your password in order to log in. This code can be sent to your phone via text message (SMS) or generated by an authentication app or hardware token.
While SMS 2FA is better than no 2FA at all, it's not the most secure option. This is because SIM swapping can give attackers access to your phone number, which means they could also intercept your 2FA codes.
For this reason, it's generally recommended to avoid using SMS 2FA whenever possible. Instead, you should use an authentication app like Google Authenticator, Microsoft Authenticator, or Authy. These apps generate unique codes that are not tied to your phone number. Hardware tokens like YubiKey are another secure option for 2FA.
To marry security and convenience, some password managers have an integrated TOTP authenticator. This lets you or your team get the one-time code you need right from your password manager!
The Problem with Social Media and SIM Swapping Scams
Many carriers still rely on security questions to verify your identity when you contact them. Unfortunately, the answers to these questions are often readily available on social media profiles. Hackers can easily find out your birthday, your pet's name, or the city you grew up in with a little social media stalking.
Here are some tips for protecting yourself:
- Be careful about what information you share on social media. Don't share your birthday, address, phone number, or the names of your pets or family members publicly.
- Use strong and unique passwords for all of your online accounts. Don't reuse the same password for multiple accounts.
- Enable privacy settings on your social media accounts. This will help to limit who can see your information.
By following these tips, you can make it more difficult for attackers to gather the information they need to carry out a SIM swap scam.
In addition to the above, here are some other things you can do to protect yourself from SIM swapping:
- Be wary of phishing scams. Don't click on links or enter your personal information into websites or emails from unknown senders.
- Review your carrier account regularly. Look for any suspicious activity, such as changes to your account information or new charges.
- Consider adding a PIN to your SIM card. This will require you to enter a PIN in order to activate the SIM card.
- Keep your software up to date. This includes your operating system, web browser, and security software.
How to manage all those unique credentials securely
Credential management and storage is tough: that's why people use passwords, security questions, and PINs that can be easily guessed, phished, or scraped from the internet.
Gain complete control and peace of mind with robust features designed for team collaboration:
- Integrated TOTP Authenticator: Generate time-based one-time passcodes directly within TeamPassword, eliminating the need for separate authenticator apps on your phone.
- Enforceable 2FA: Mandate two-factor authentication for every user across your organization, ensuring a consistent and high standard of security.
- Detailed Activity Logs: Maintain full visibility with a complete audit trail of who accessed what and when, perfect for security audits and accountability.
- Unlimited Records & Groups: Store an infinite number of logins and organize them into logical groups by team, project, or client for easy access and management.
- Multiple User-Roles: Assign granular permissions to control exactly who can view, edit, and create credentials, ensuring access is granted only where it's needed.
- Free Google Sign-In: Simplify onboarding and daily access with secure, one-click login using your team's existing Google accounts.
- One-Time Share: Securely share a single password with an external contractor or partner for a limited time, without giving them permanent access to your records.
With straightforward plans starting at $2.41 per user per month, TeamPassword is the most effective and affordable way to protect your business.
Try TeamPassword for free for 14 days with no obligations.