What Can Hackers Do with your Email Address?
For many of us, platforms such as Slack, Telegram, and social media have eclipsed our email address as the home base from which all our online communication happens. Nonetheless, to sign up for their services, these platforms require one thing in common: our email.
Email is still considered an authoritative source of identity check. It is used for password resets, 2FA authorization, backup verification for other emails…the list goes on. Friends and family don’t think twice when they receive an email from you unless the content is demonstrably suspicious.
Recent reports show that email scam is the costliest type of cybercrime, with nearly $2.4 billion being stolen in 2021 alone. Part of the reason for its success relative to other scams and cybercrimes is that email scam has become quite sophisticated. We know to hang up the phone when "Microsoft Support" calls to get remote access to our laptop so they can remove that virus that we didn't know we had.
We’re going to cover 5 nefarious things hackers can do with your email address, and 5 actions you can take right now to protect yourself.
Table of Contents
5 ways a hacker can exploit your email address
We spread our email addresses across the web each time we create an account or communicate online. Soon, they disappear beyond our knowledge or reach, either because we forget to whom we’ve given them or through leaks and breaches. We think of our email address as something fairly public; it's hard to do anything online without it.
Once you understand how your email can be exploited, you’ll be equipped to use the tips at the end of this article to keep yourself safe.
Cybercriminals have plenty of reasons to want your email. As Mika Aalto told Spiceworks, “Every breach begins with a malicious email.”
1. Spoof your email address to scam friends and family
Email spoofing is a scam where attackers manipulate email headers or use look-alike addresses to trick recipients into believing the message is from a trusted source. Here are common spoofing techniques:
1. Manipulated Email Headers
Scammers alter the email header to make it appear as though the message is coming from a legitimate domain (e.g., [email protected]), even when it’s not.
2. Look-alike Addresses
Attackers create email addresses that closely mimic legitimate ones, relying on subtle visual tricks to deceive you.
-
Example 1: [email protected]
- Scammers use the letters “r” and “n” together to imitate “m”. Unless you’re consciously checking, your brain might auto-correct the address.
- Tool Tip: Use a Unicode Inspector to catch look-alike foreign characters or other manipulations.
-
Example 2: [email protected]
- While lowercase emails are standard, attackers may exploit capitalization to obscure differences. Here, the lowercase “L” is mistaken for an “i”.
How to Spot and Protect Against Spoofing
- Check the Email Address: Hover over the sender's name or email address to reveal its true form.
- Use Tools: A Unicode Inspector helps spot visually similar characters.
- Educate Yourself: Watch detailed tutorials like this video by ThioJoe to see spoofing techniques in action:
Email spoofing is a gateway to phishing attacks, financial fraud, and malware delivery. Awareness and vigilance are your best defenses.
2. Hack into your online accounts
Your email is often the foundation of your online identity, serving as the key to most of your accounts. If compromised, it can lead to widespread damage.
Why Your Email Matters
- Email as a Master Key: Most online accounts rely on your email for login credentials and password recovery.
- The Risk of Single Points of Failure: Using the same email for everything makes you more vulnerable to attacks.
Common Cyberattack: Credential Stuffing
- What Is It? Hackers use your email in combination with stolen or guessed passwords to attempt logins on multiple platforms.
- How It Happens: Once an attacker confirms your email, they use automated tools to test it against thousands of password combinations.
How to Protect Yourself
-
Diversify Your Emails:
- Use at least four separate email addresses for:
- Banking and finances
- Shopping and subscriptions
- Social media
- Other miscellaneous accounts
- This reduces the fallout if one email gets compromised.
- Use at least four separate email addresses for:
-
Never Reuse Passwords:
- Each account should have a unique, strong password to prevent cascading breaches.
-
Enable 2FA (Two-Factor Authentication):
- Always use the strongest 2FA option available, such as an authenticator app or hardware key, for added security.
3. Gather personal information to socially engineer you or others
Your email reveals more about you than you probably think. It can be used to track down anything from your social media to Spotify account and where you work. Once a hacker matches your phone number to your email, they're ready to run a sophisticated social engineering attack. With enough personal information harvested, they can convincingly impersonate you or someone you know through spoofing. And if they hack all the way into your email, they can send convincing emails as you.
Your email address can also be used on the dark web to identify and purchase relevant leaked and stolen personal information.
- Check sites like haveibeenpwned to see if your information is out there.
- Real-time monitoring is also available through services such as Echoset.net.
4. Hack your personal email and jeopardize your online and in-person life
Given that email is the primary identifier and source for password resets, if someone hacks your email they can typically reset the passwords for ALL your online accounts. Once into an account, they can often change the associated email address with the click of a button - and you can say goodbye to that account forever.
The cybercriminal will also be able to see tickets and hotel reservations that come to your email. Assuming they’ve scraped your home address, they can use this information to make a move on your personal property.
5. BEC (business email compromise)
Cybercriminals may simply want to use you as a gateway to your company. According to the FBI, BEC is one of the most financially damaging online crimes.
There are several possible avenues to breach a company. One common tactic in a BEC attack is to send an urgent email posing as the CEO or other executive. The employee, fearing retribution, ignores otherwise suspicion-arousing signs of a scam and cooperates with the directive, or at the very least opens the attachment or clicks the link. This may be all the attacker needs to gain a foothold.
Make it clear to everyone you work with that treating anything other than face-to-face communication with an extra helping of caution will never be punished. You need your team on your side when it comes to keeping your business safe.
How do I protect my email?
1. Set up 2FA
Use 2FA to maximize security for your email accounts. Of course, we recommend using 2FA on all accounts that allow it - even “unimportant” ones. Security experts recommend using time-dependent codes through apps such as Authy when possible, as they are much more difficult to get ahold of than SMS-based 2FA.
Many email providers support physical security keys such as Yubikey if you want to take 2FA to the next level.
2. Don’t reuse passwords
While the advice to “use unique, strong passwords” is crucial, it’s not practical to create and remember dozens of complex passwords on your own. This is where a password manager becomes an essential tool.
A password manager generates, stores, and automatically fills in strong, unique passwords for all your accounts. This solves the problem of password reuse and removes the burden of memorization.
When choosing one, consider your needs:
-
For collaborating with colleagues or sharing with family, look for a team-based manager built for secure sharing. TeamPassword, for example, is designed for this purpose.
-
For personal use, many excellent free or low-cost options are available that can secure your individual accounts.
The most important step is to choose a reputable manager and commit to using it. The initial setup is a small investment of time that pays massive dividends in security.
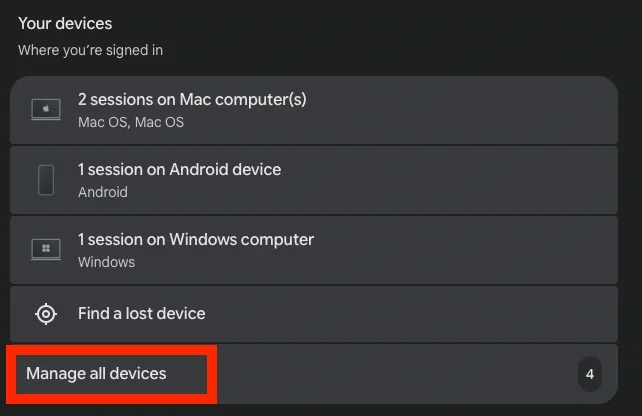
3. Check what devices are signed into your email
For Google accounts:
- Go to https://myaccount.google.com/
- click on Security and Sign-in
- scroll down to Your devices
- Click Manage Devices
Now, sign out that old laptop you’ve got sitting in a drawer that hasn’t been updated in 3 years, and remove your parent’s desktop that you used to check email once. In general, check that you recognize all device activity. The only devices with access should be ones whose security you control.
4. Check data breach reports
Check sites such as haveibeenpwned to see if your email or passwords are part of any breaches or leaks. If your email address has been significantly impacted, you may need to migrate to a new address. Real-time monitoring is available through services such as Echosec and Whatsup Gold.
Once your email address, passwords, or personal documents are out there, the best you can do is take appropriate reactive steps to minimize the possibility of that information being used against you.
- If your email is the culprit, immediately change all passwords on connected accounts. Cybercriminals will use your email to credential stuff thousands of online accounts in the off chance that they can break in. Seriously, don't reuse passwords.
- If your driver's license, passport, or SSN numbers were leaked, report this to your local DMV, U.S. State Department, and Social Security Administration, respectively.
To avoid being impacted by basic data leaks, look into setting up temporary aliases for use with different online accounts so you can more easily identify when and where you’ve been compromised.
5. Practice (close to) Inbox Zero
Even if you’re not ready to fully commit to the inbox zero lifestyle, you can utilize many of its strategies to greatly reduce stress around handling emails. If your inbox is out of control, you may miss a suspicious login attempt or password reset message. Plus, if you’re stressed and pressed for time when sorting through your emails, you’re less likely to exercise the caution and attention to detail required to catch spoofed emails and false links.
Here are some tips for Inbox Zero to get you started:
- Set aside dedicated time for email: Avoid constant checking throughout the day. Schedule specific times to tackle your inbox.
- Process emails in batches: Instead of reacting to each email individually, review them in groups to improve efficiency.
- Develop a triage system: Quickly categorize emails as "delete," "archive," "respond," or "defer."
- Utilize filters and labels: Organize your inbox with filters for specific senders or subjects, and use labels for easy categorization.
- Unsubscribe from unwanted emails: Reduce clutter by unsubscribing from newsletters and promotional emails you no longer find valuable.
- Practice the 2-minute rule: If an email can be responded to in two minutes or less, do it immediately.
FAQS:
What can a hacker do with just my email address and not my password?
- Send phishing emails to your contacts, pretending to be you and asking for money, personal information, or malicious links.
- Sign-up for unwanted services or subscriptions that may charge you fees or send you spam.
- Use your email address to learn more about you, such as your name, location, interests, or online activity.
Can my email account be hacked without a password?
Yes, your email account can be hacked without a password if you click on a malicious link, download an infected attachment, or use a compromised public Wi-Fi network. Hackers use these methods to access your email account and steal your personal information or send spam messages from your account. To prevent this, always use a strong password, enable two-factor authentication, avoid suspicious emails and websites, and use a secure VPN when connecting to public Wi-Fi.
How much info can a hacker get from just my email address?
A threat actor can discover your name, location, online accounts, contacts, and even your SSN if your email address was part of a serious breach. They can use this information to launch phishing attacks, spam you, steal your identity, or compromise your security. Check haveibeenpwned to see if your email was leaked.
How do hackers get into accounts without a password?
- Phishing: Sending fake emails or websites that look legitimate and asking you to enter your password or other sensitive information.
- Social engineering: Tricking you into giving away your password or other credentials by pretending to be someone you trust or someone who needs your help.
- Malware: Installing malicious software on your device that records your keystrokes, steals your data, or gives the hacker remote control over your device.
- App permissions: Exploiting apps that you have authorized to access your account and use them to post, send, or change things on your behalf.
To protect yourself from these attacks, you should use different passwords for different accounts, use a password manager, enable two-factor authentication on your email, avoid clicking on suspicious links or attachments, update your software regularly, and revoke access to apps that you don't use or trust.
How does TeamPassword keep your email and accounts safe?
If using password best practices is too hard neither you nor your team will do it. TeamPassword makes it easy to store, update, and share credentials without them leaving an encrypted environment.
Storing your login credentials in a password manager minimizes damage in the event that your email gets breached. People who don’t use a password manager may store passwords in an excel spreadsheet which they email to others, or a Google Sheet which can be accessed if their Google account is compromised.
TeamPassword is the ultimate password manager tailored for small businesses and digital marketing agencies. We understand the daily struggle of managing passwords and ensuring secure team access. Our solution offers flexible password management to fit your unique business needs.
- Integrated TOTP Authenticator: Generate time-based one-time passcodes directly within TeamPassword, eliminating the need for separate authenticator apps on your phone.
- Enforceable 2FA: Mandate two-factor authentication for every user across your organization, ensuring a consistent and high standard of security.
- Detailed Activity Logs: Maintain full visibility with a complete audit trail of who accessed what and when, perfect for security audits and accountability.
- Unlimited Records & Groups: Store an infinite number of logins and organize them into logical groups by team, project, or client for easy access and management.
- Multiple User-Roles: Assign granular permissions to control exactly who can view, edit, and create credentials, ensuring access is granted only where it's needed.
- Free Google Sign-In: Simplify onboarding and daily access with secure, one-click login using your team's existing Google accounts.
- One-Time Share: Securely share a single password with an external contractor or partner for a limited time, without giving them permanent access to your records.
Give TeamPassword a try for free and let us know what you think!
Enhance your password security
The best software to generate and have your passwords managed correctly.